By Dan Byrne for AMLi
POLICE across Europe and the eastern US have cracked down on the central European gang QQAAZZ laundering tens of millions of euro from hacking and cyber attacks.
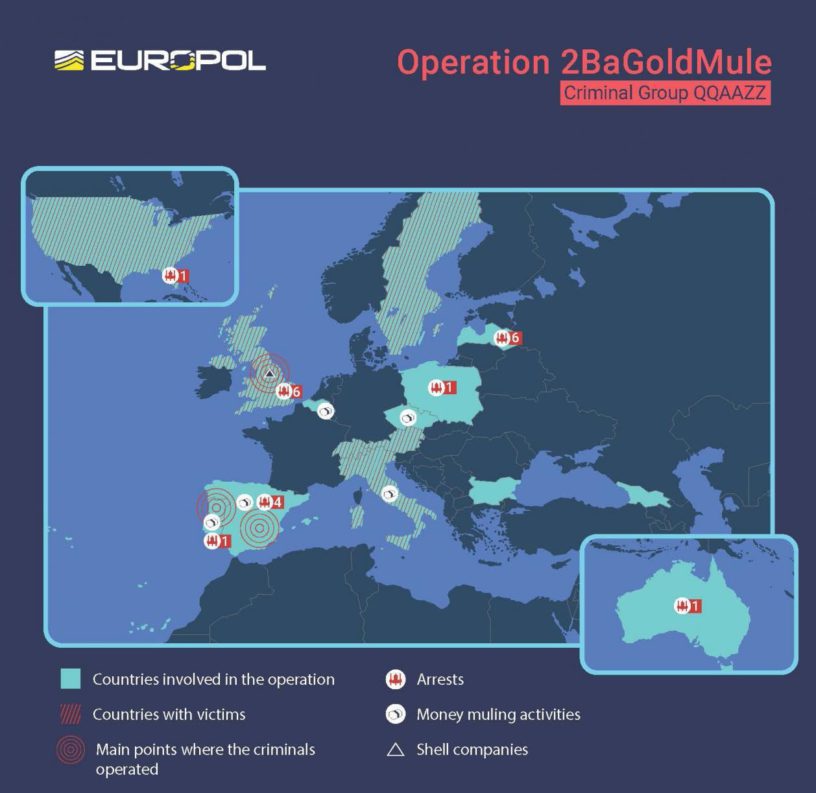
The operation across 16 countries led to 20 arrests of gang suspects who were washing the proceeds of cyber attacks through personal and corporate bank accounts on behalf of some of the world’s most notorious cybercriminals.
The cyber gangs behind some of the world’s most harmful malware attacks – Dridex, Trickbot, GozNym – feature among those who benefited from money laundering activity of QQAAZZ.
EUROPOL
Around 40 house searches were carried out in Latvia, Bulgaria, the United Kingdom, Spain and Italy, with criminal proceedings initiated against those arrested by the United States, Portugal, the United Kingdom and Spain.
The largest number of searches in the case were carried out in Latvia in operations led by the Latvian State Police (Latvijas Valsts Policija). Bitcoin mining equipment was also seized in Bulgaria.
The QQAAZZ network opened and maintained hundreds of corporate and personal bank accounts at financial institutions throughout the world to receive money from cybercriminals who stole it from accounts of victims. The funds were then transferred to other QQAAZZ-controlled bank accounts and sometimes converted to cryptocurrency using “tumbling” services designed to hide the original source of the funds.
EUROPOL
“The QQAAZZ members secured these bank accounts by using both legitimate and fraudulent Polish and Bulgarian identification documents to create and register dozens of shell companies which conducted no legitimate business activity,” Europol said in a statement.
“Using these registration documents, the QQAAZZ members then opened corporate bank accounts in the names of the shell companies at numerous financial institutions within each country, thereby generating hundreds of QQAAZZ-controlled bank accounts available to receive stolen funds from cyber thieves,” the statement added.
“After taking a fee of up to 50-percent, QQAAZZ returned the balance of the stolen funds to their cybercriminal clientele,” said Europol whose EC3 unit co-ordinated the raids. The operation was codenamed “2BaGoldMule.”
The Organised Crime Group (OCG) is made up of several layers of members mainly from Latvia, Georgia, Bulgaria, Romania and Belgium.
Europol said the investigation was led by the Portuguese Judicial Police (Polícia Judiciária). Others involved were Pennsylvania prosecutors, the FBI alongside the Spanish National Police (Policia Nacional) and the regional Catalan police (Mossos D’esquadra). Police from the UK, Latvia, Bulgaria, Georgia, Italy, Germany, Switzerland, Poland, Czech Republic, Australia, Sweden, Austria and Belgium also participated.
It is estimated the QQAAZZ network laundered, or attempted to launder, tens of millions of euros in stolen funds since 2016.
AMLi understands that QQAAZZ advertised its services as a “global, complicit bank drops service” on Russian-speaking online cybercriminal forums where cybercriminals gather to offer or seek specialised skills or services needed to engage in a variety of cybercriminal activities.
The criminal gangs behind some of the world’s most harmful malware families – Dridex, Trickbot, GozNym – feature among those having benefited from the services provided by QQAAZZ.
Europol’s European Cybercrime Centre (EC3) co-ordinated the operation from its HQ in the Hague, Holland.
Edvardas Šileris, Head of EC3 Thursday said: “Cybercriminals are constantly exploring new possibilities to abuse technology and financial frameworks to victimise millions of users in a moment from anywhere in the world. Today’s operation shows how through a proper law enforcement international coordination we can turn the table on these criminals and bring them to justice.”
In the US meanwhile 14 members of the OCG have been charged in the US for involvement in an international cybercrime and laundering operation.
An FBI agent involved in the case said that the related investigation had been going on for years and that it had “implications around the world.”
The QQAAZZ members who were charged have been linked to the laundering (or attempted laundering) of tens of millions of dollars in funds stolen by cybercriminals, the DoJ said on Thursday.
QQAAZZ itself has been under suspicion for this kind of activity by multiple law enforcement agencies for years, principally the DoJ and Europol.
“We will be relentless in our pursuit of cybercriminals regardless of where they reside,” said US attorney Scott W. Brady of Pennsylvania – where the suspects have been charged.
“Our message to money laundering organisations like QQAAZZ is simple: international borders will not stop the dedicated efforts of law enforcement across the globe to bring you to justice.”
Tackling financial crime through co-operation across borders has been a major talking point in AML debates for some time, with politicians and banking officials urging for more international cooperation since criminals already work at that level.
The DOJ highlighted that the QQAAZZ’s services have been used by some of the world’s most notorious malware families and associated criminal gangs.
It praised the work of partner law enforcement groups in countries such as the UK, Germany, Switzerland, and Latvia – where it said that the highest number of searches and arrests were carried out.
Share this on:
Follow us on: